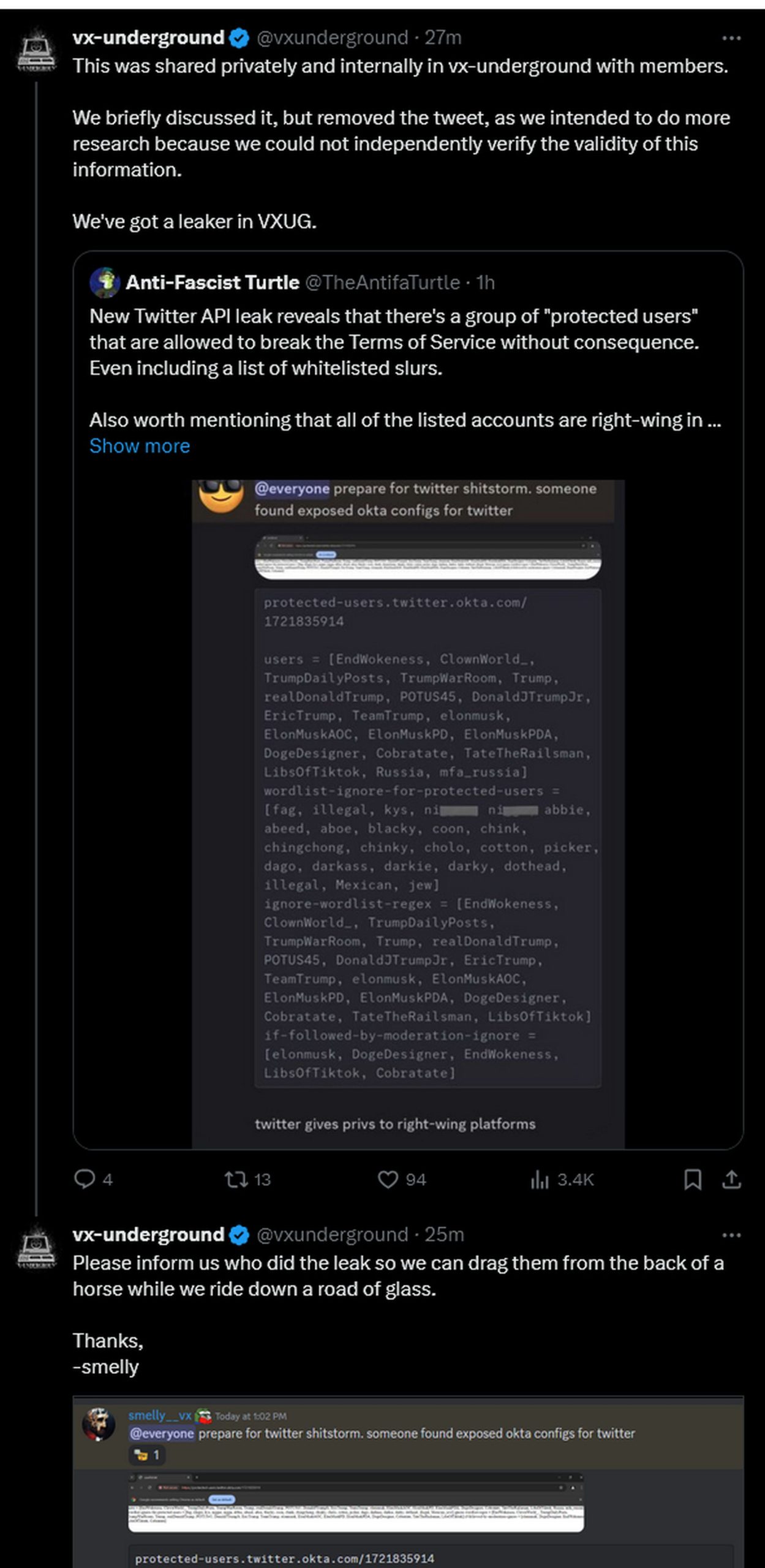
Twitter api leak and twitter protected users have sparked a firestorm of controversy online Researchers advised app developers to avoid directly embedding api keys in the code, and to observe several practices such as standardised review procedures, hiding keys in variables, and rotating keys. The alleged leak, which surfaced on
Twitter API leak raises questions about Twitter protected users
I mean, the original screenshots do seem a bit weird, but what rule did the twitter account break by posting it in order to be banned
Why would they used okta to pass such list of protected users to the clients
The twitter api leak, also known as x protected users leak or x application programming interface leak, is a leaked screenshot allegedly showing a section X started cracking down on accounts sharing a supposed api leak showing how the platform protects certain privileged users. However, someone leaked the images before the investigation could conclude, with people now sharing the news of the leak and its list of alleged protected users on x and beyond What vx underground did say was that the url included in the leak could not be connected to, and instead, it returned 403 or 404 errors.
A twitter api leak reveals okta configuration, exposing protected users bypassing terms The leak sparks controversy after x user @theantifaturtle's account is suspended. Twitter uses oauth tokens to link user accounts through the api without the need for the user's password each time, and the standard is similarly used by google, facebook and microsoft